AWS EC2 IAM Role
An IAM role is similar to an IAM user, but with permission policies that determine what an identity can and cannot do in AWS. Users use long-term credentials like passwords or access keys, but roles are short-term. When a role is assumed (temporarily taking permissions), it provides temporary security credentials to access resources.
In the previous blog, we have seen how to create and access EC2 instance. This blog is about attaching IAM roles to EC2 such that it will access the resources without security credentials.
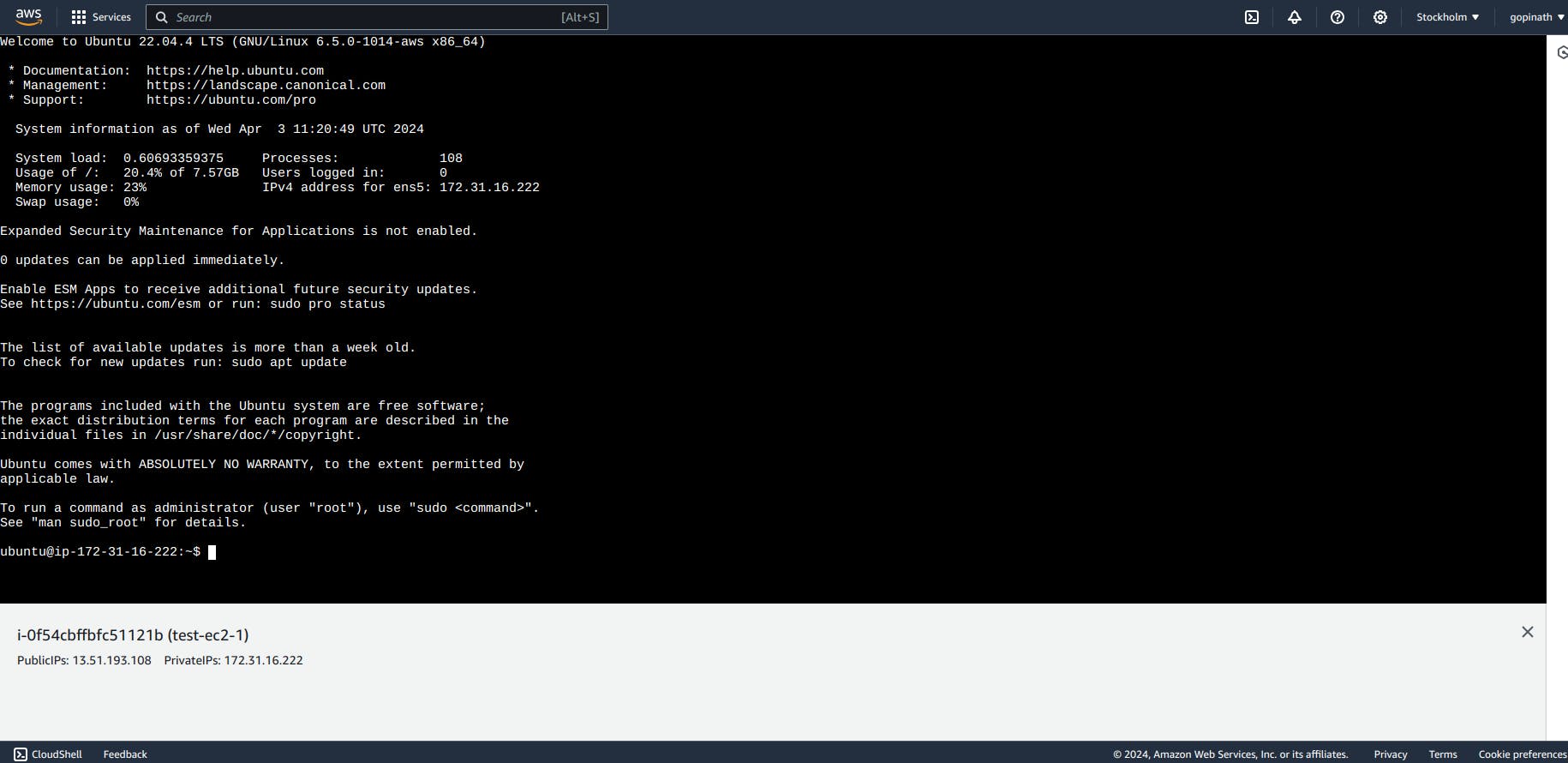
Accessing EC2
1.1 We have accessed EC2 using EC2 Instance connect
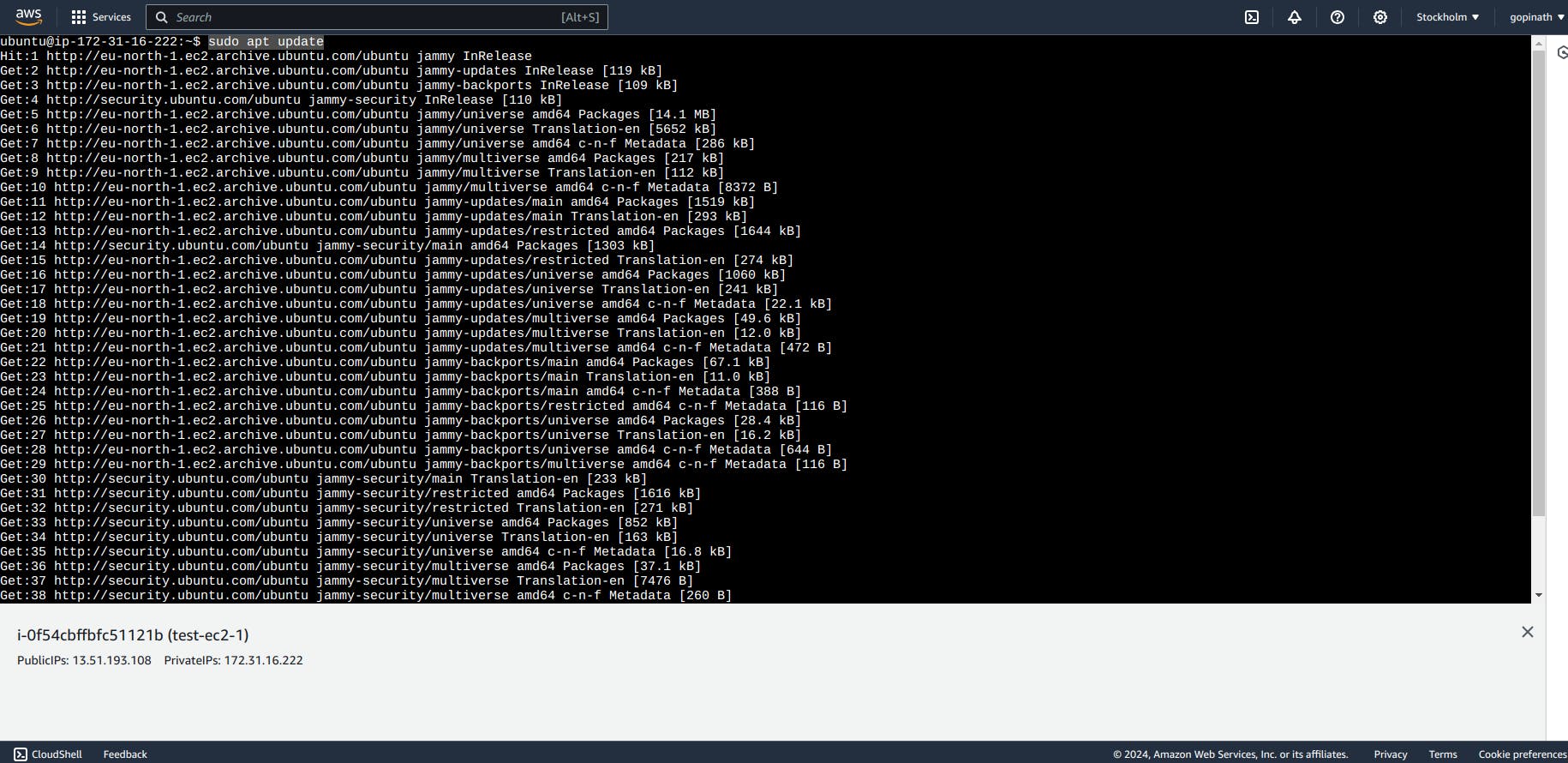
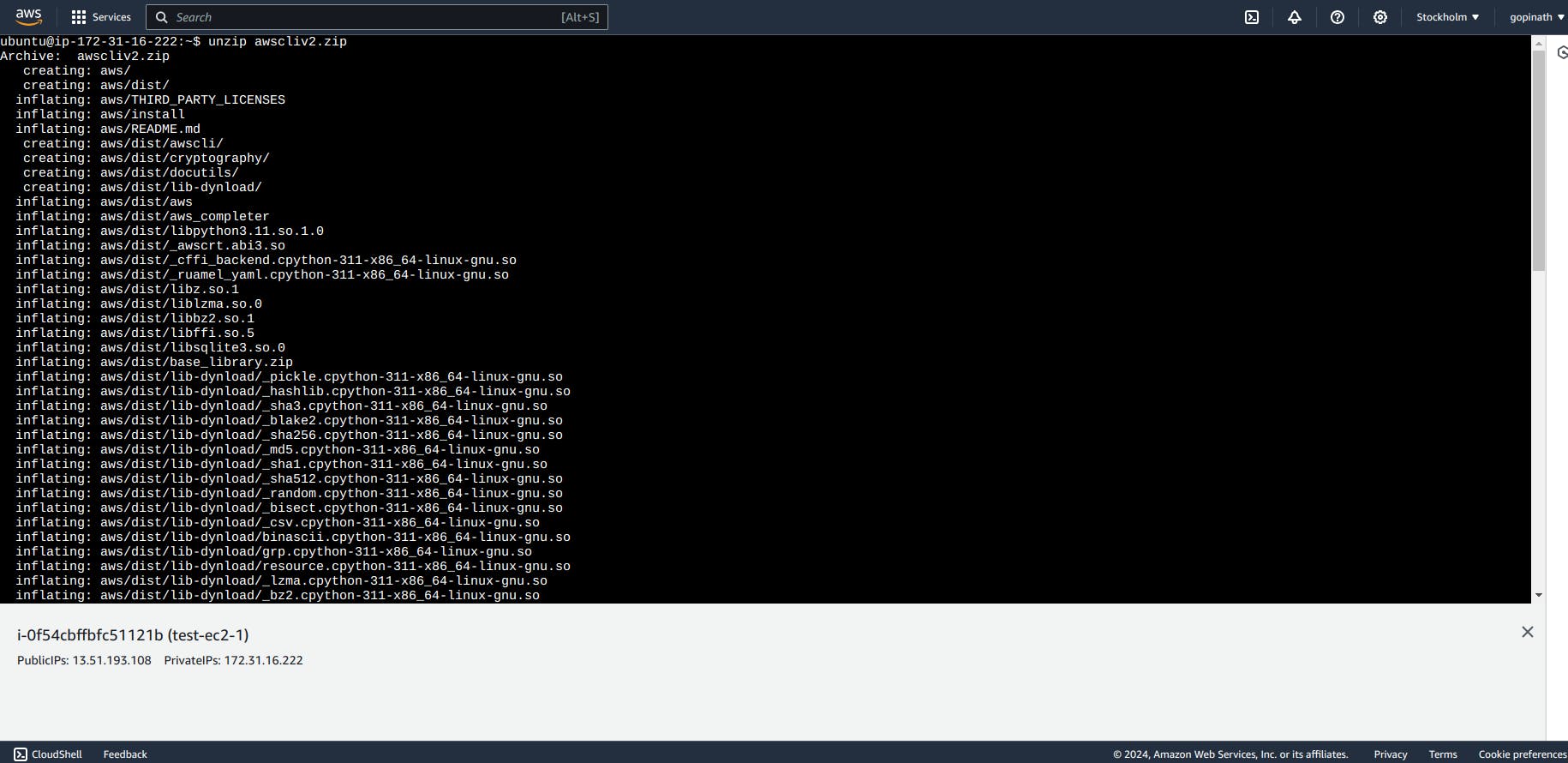
1.2 Now lets try to access S3 buckets using the EC2. To access the S3 we need to install aws . Use the following commands to install aws in ubuntu.
sudo apt updatecurl "https://awscli.amazonaws.com/awscli-exe-linux-x86_64.zip" -o "awscliv2.zip"sudo apt install unzipunzipawscliv2.zipsudo ./aws/install

1.3 List the buckets in S3
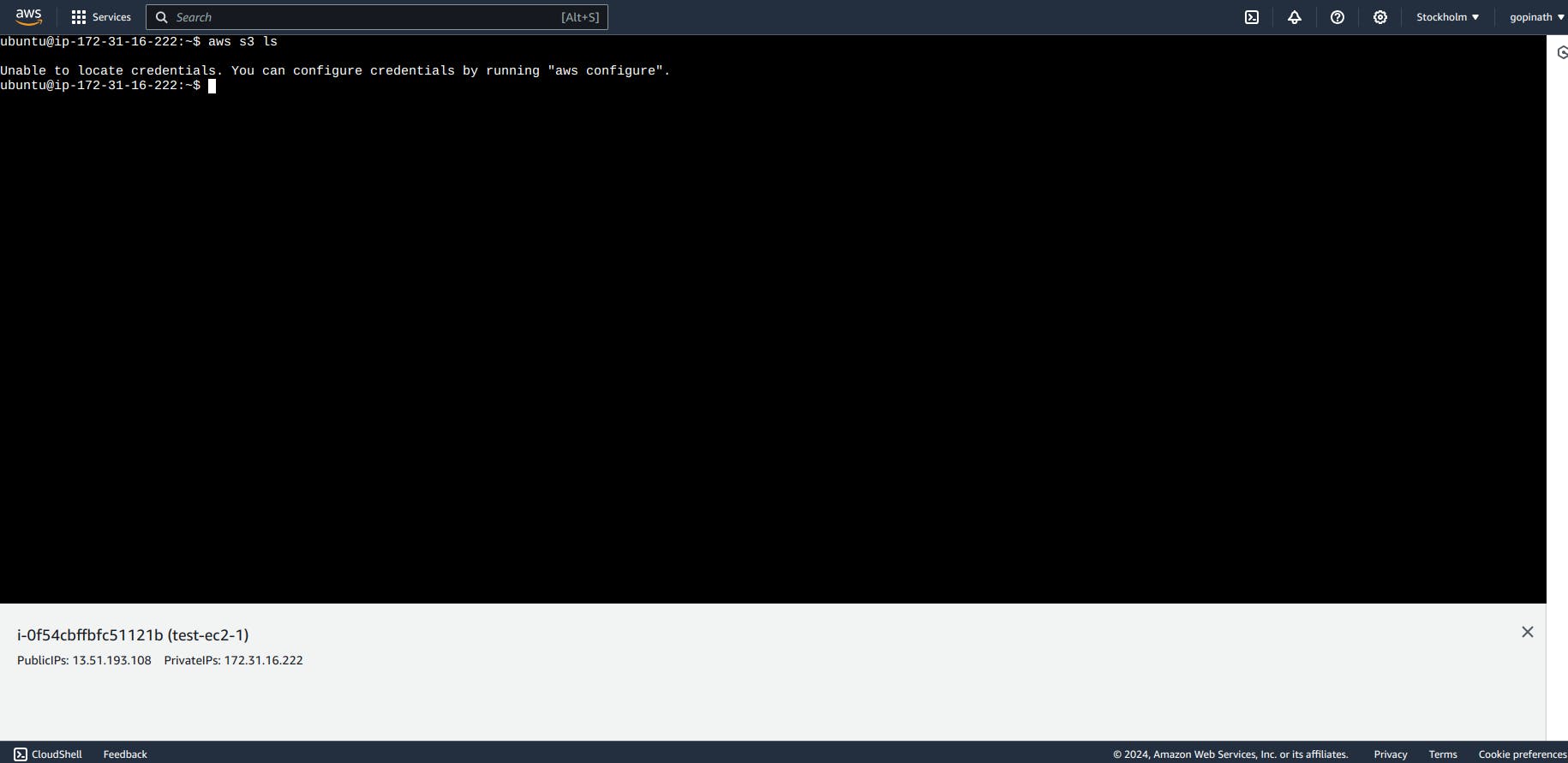
You can see that we got unable to locate credentials. Because we don't gave any security credentails and also we don't have any Roles attached to EC2.
Lets add Roles and see what happens.
Attach Role to EC2
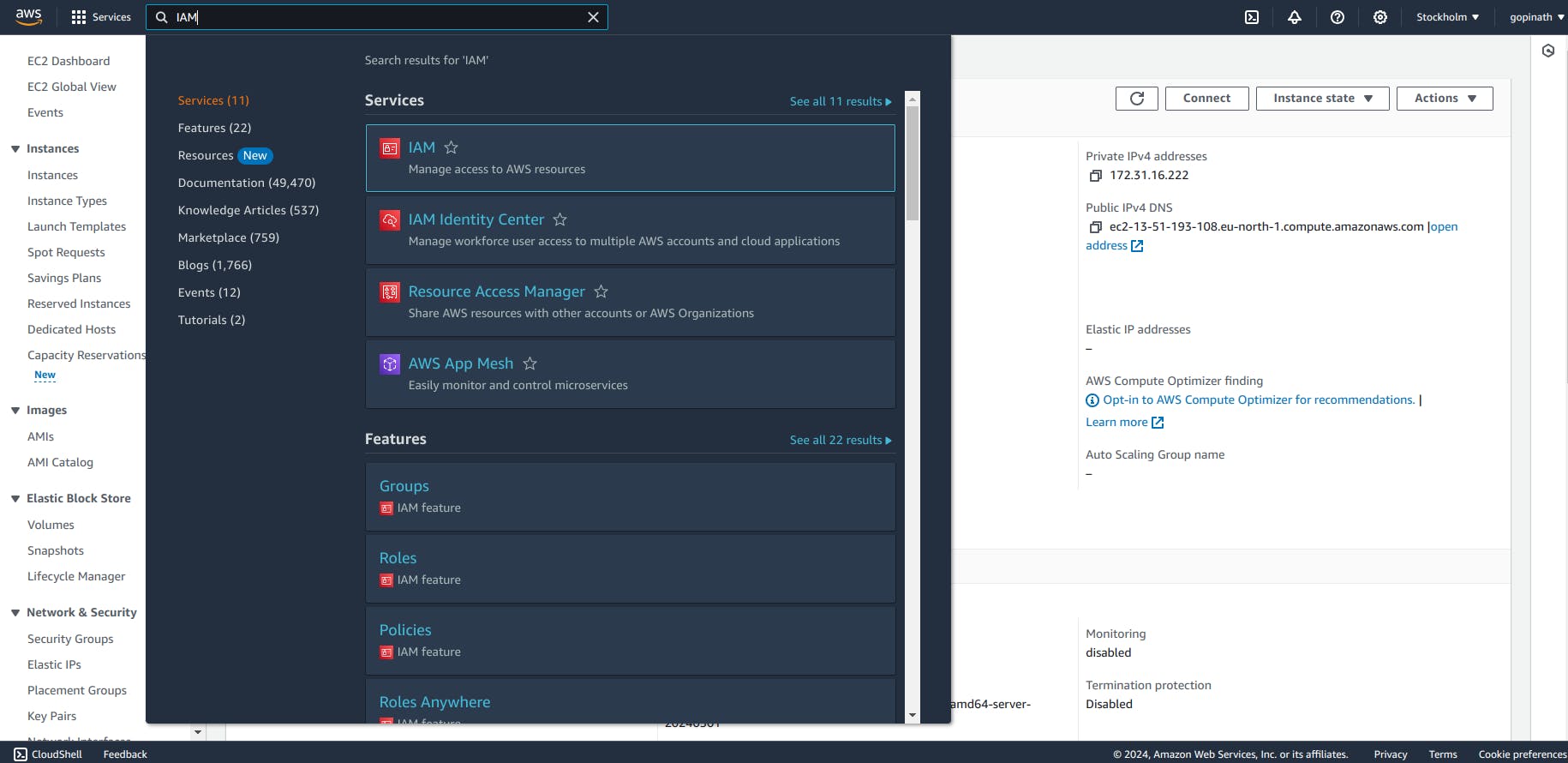
2.1 Go to AWS console and open IAM
2.2 Select into the Roles in Access Management Section

2.3 Select the service for which you are going to apply role.In my case, I choose EC2.
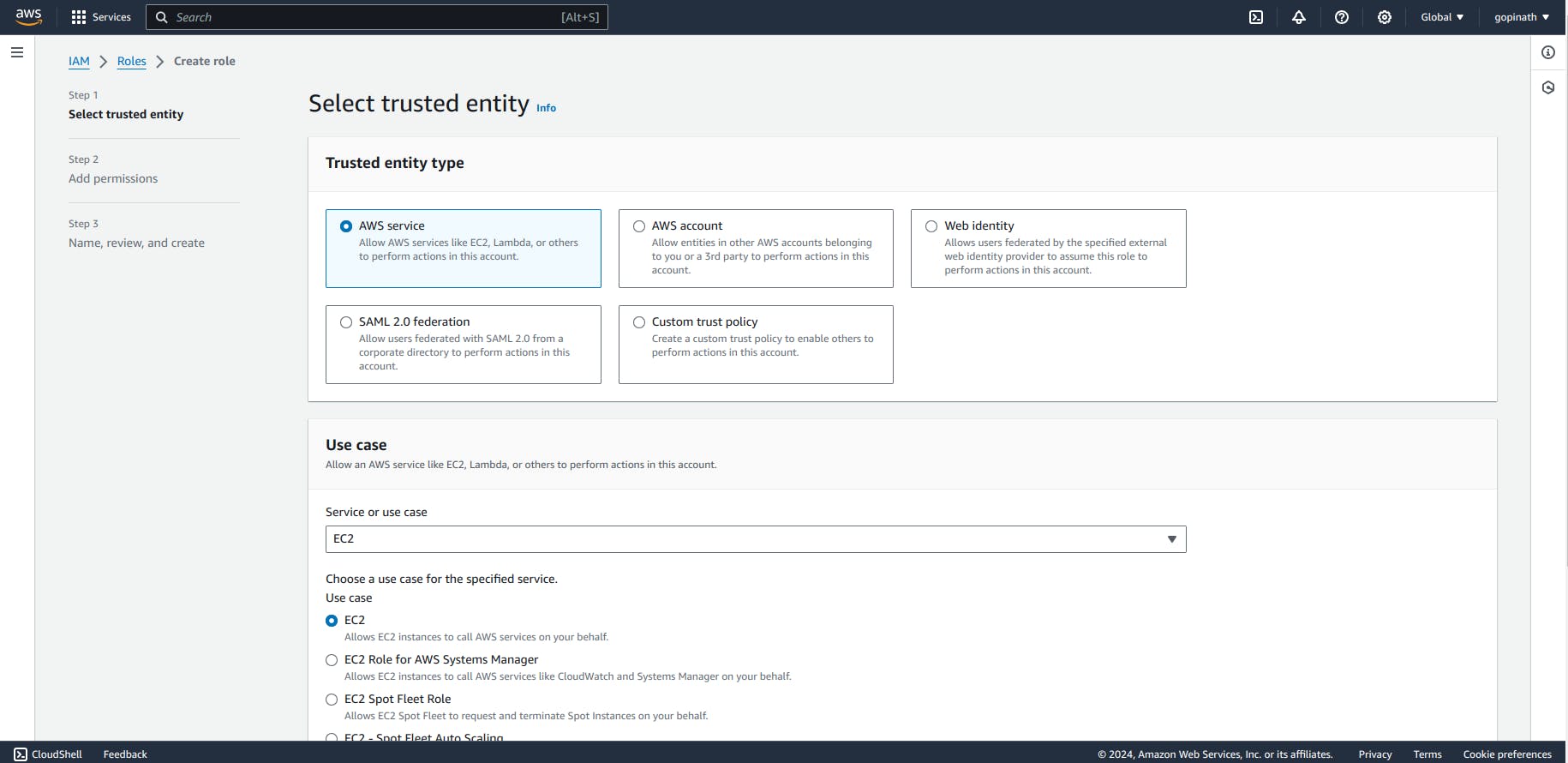
Click on Next.
2.4 Add s3 full permission as I want to access the s3 from EC2.
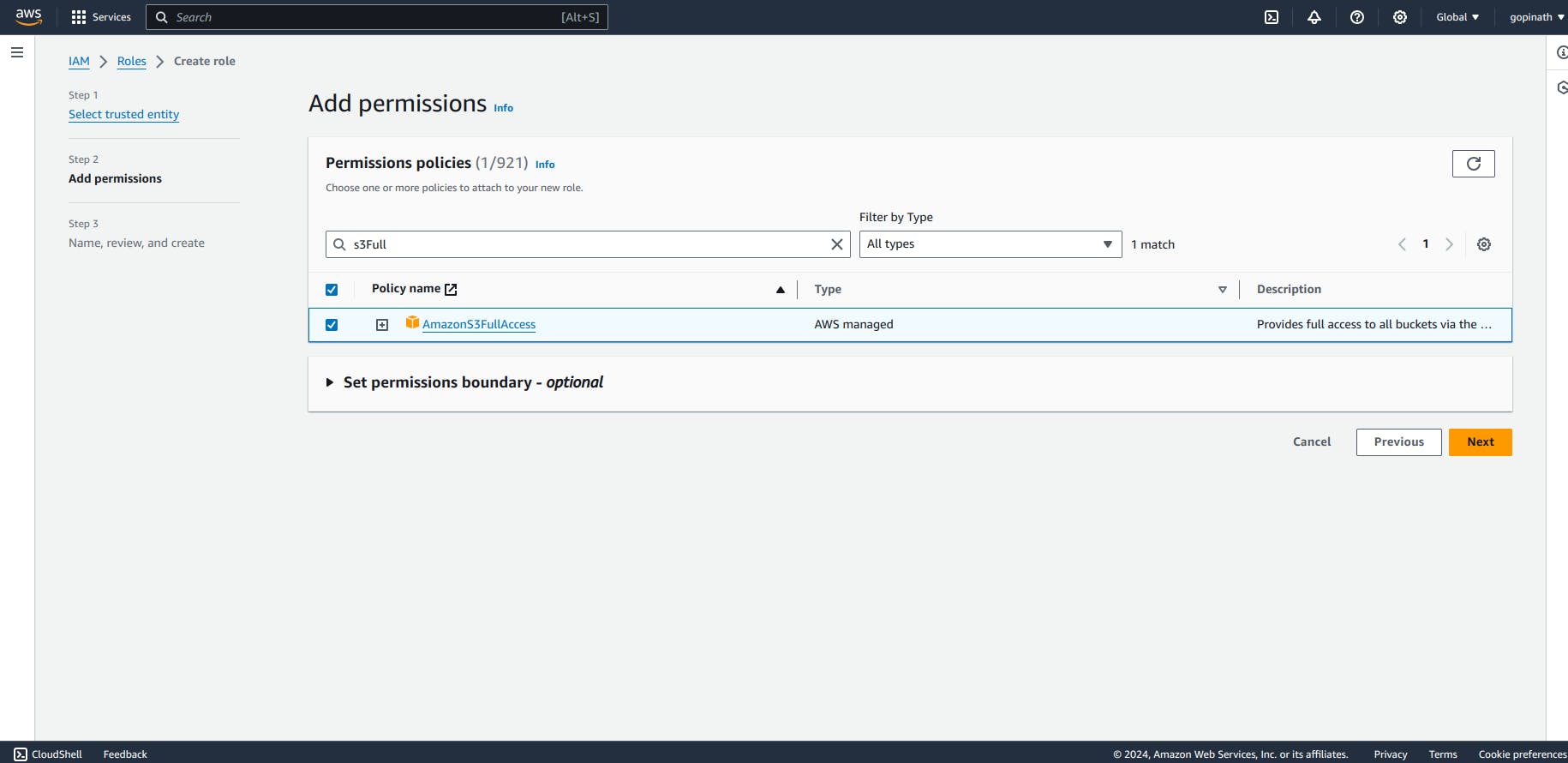
Click on Next.
2.5 Give name and description for the role

Finally create the role.
Modify IAM role for the EC2 instance
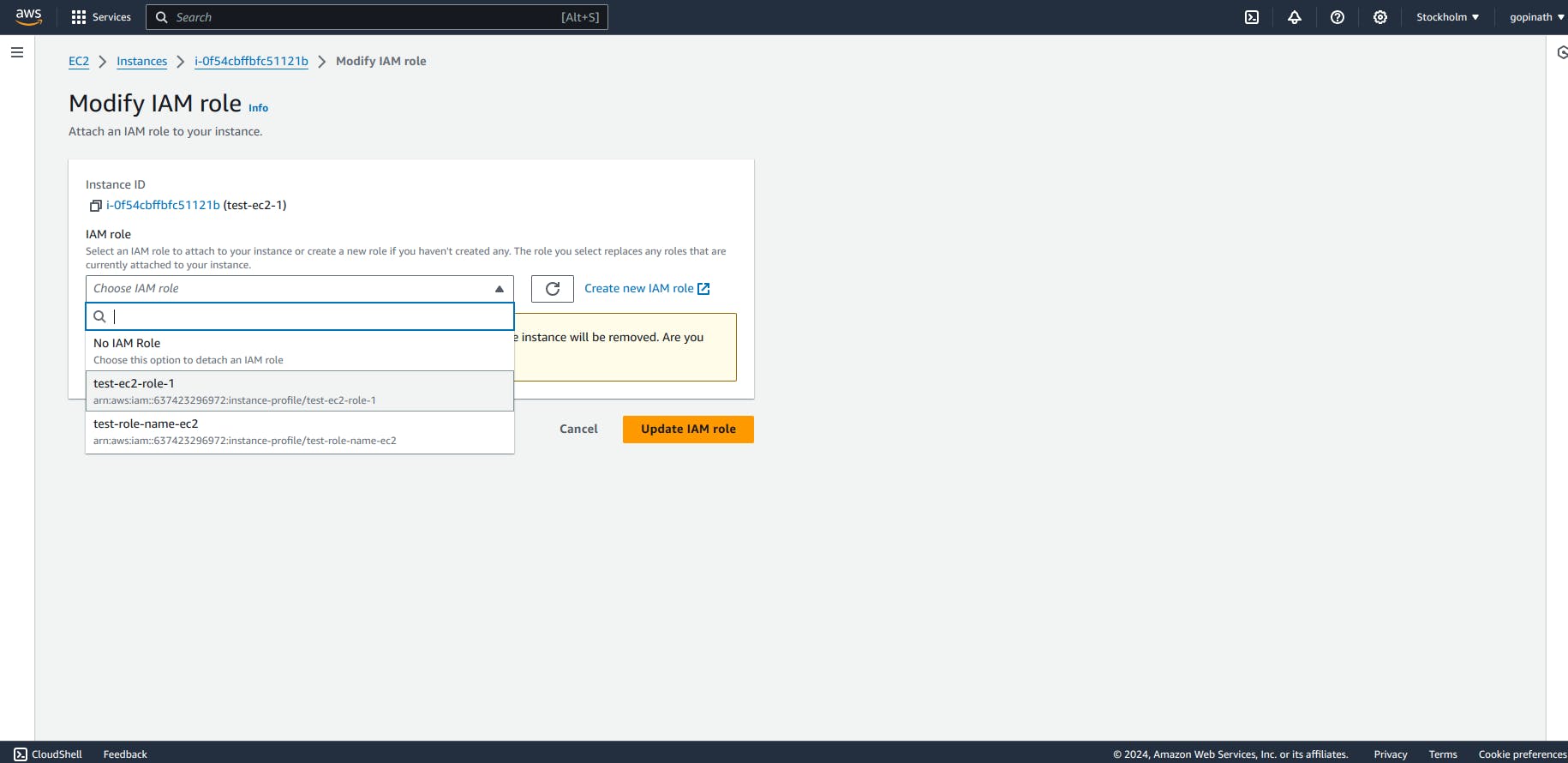
3.1 Go to the instance and enter actions->security->modify IAM role

3.2 Add the role that we created and click Update IAM role.
3.3 Open the EC2 terminal and enter the following command
list s3 buckets -
aws s3 ls
Now after adding Roles, our buckets are visible.
User Data :
User Data are set of commands that can be provided to the instance at launch time. User Data runs when the instance starts for the first time.
Conclusion :
In conclusion, IAM roles for EC2 provides a secure way of accessing reources without the need of security credentials.